Malware analysis Malicious activity
4.9
$ 37.99
In stock
(275)
Product Description

Remove Your System Is Damaged By Malicious Activity Pop-ups
Highlight, take notes, and search in the book

Mastering Malware Analysis: A malware analyst's practical guide to combating malicious software, APT, cybercrime, and IoT attacks, 2nd Edition
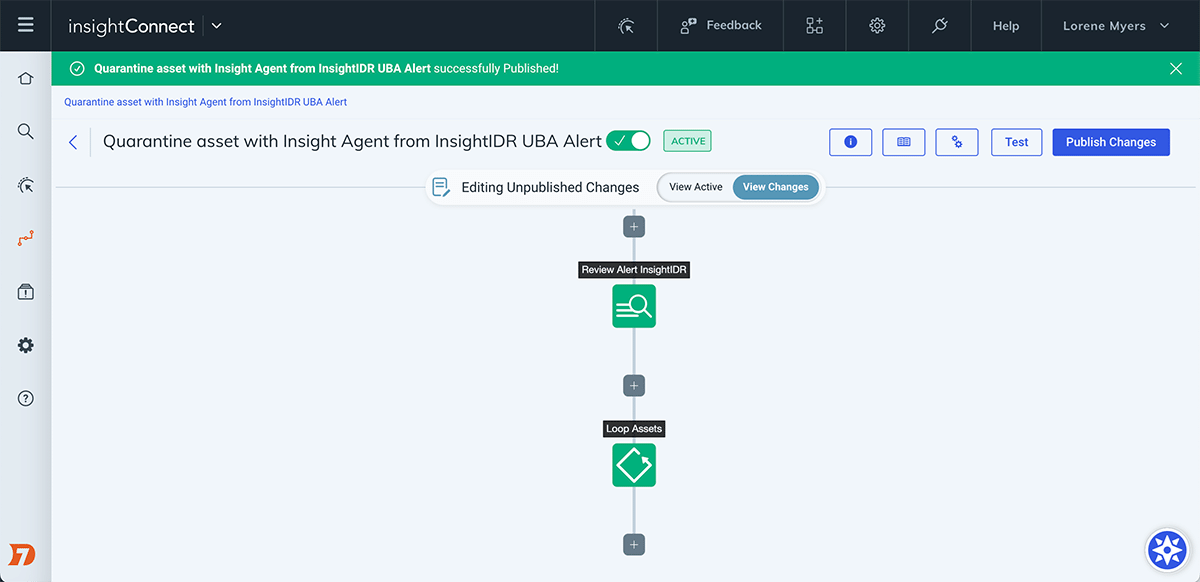
Automate the Investigation and Containment of Malware: InsightConnect

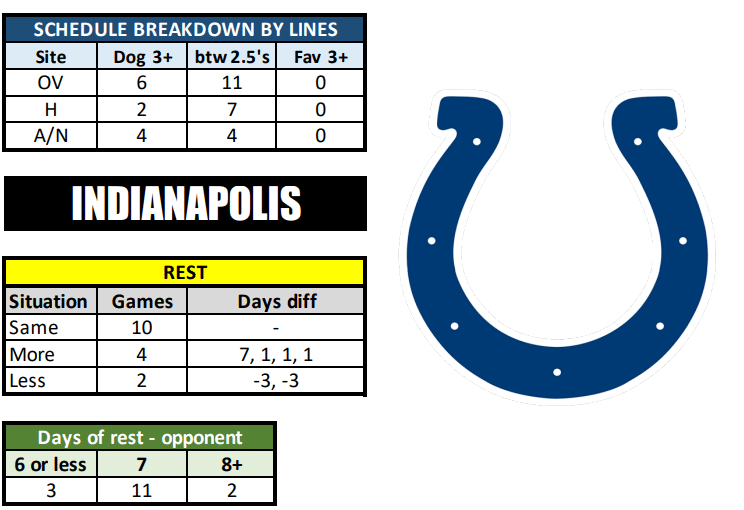
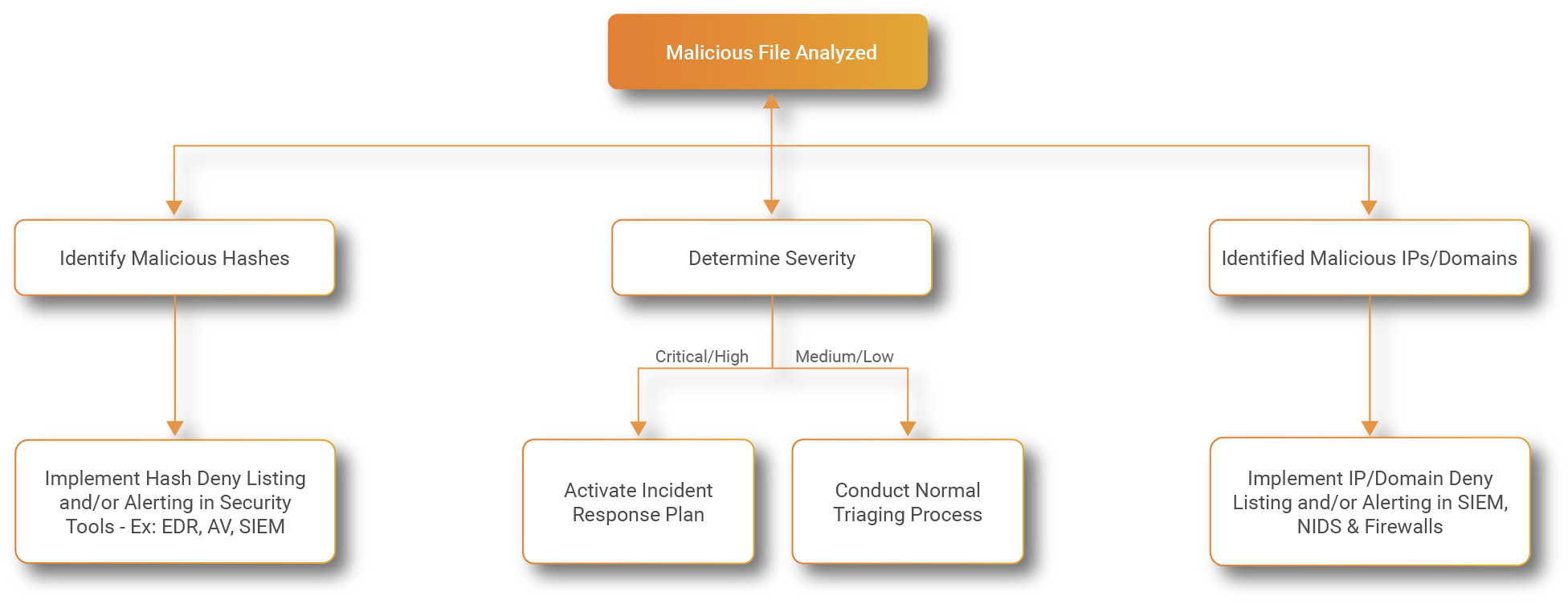
A flow chart of malware detection approaches and features

Structure of static malware analysis
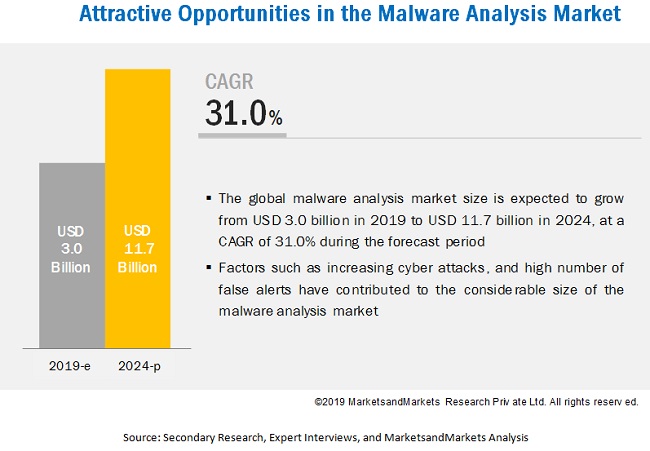
Malware Analysis Market Growth Drivers & Opportunities
Malware Analysis: Protecting Your Network from Cyber Attacks
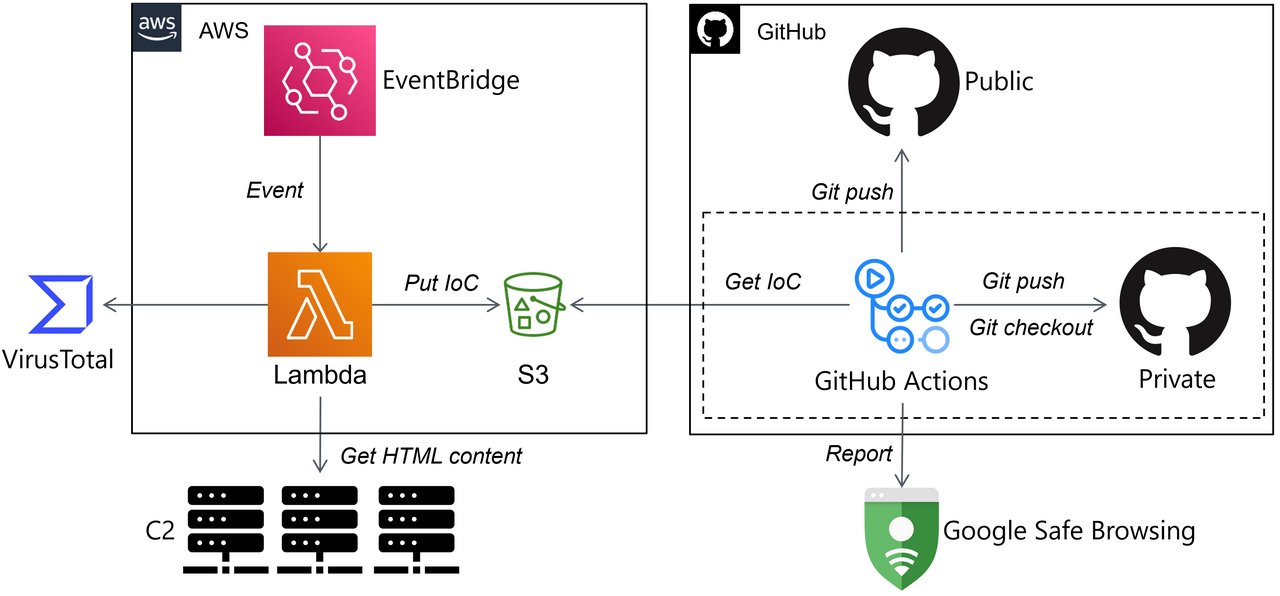
Automating Malware Analysis Operations (MAOps) - JPCERT/CC Eyes

What is Malware Analysis

Advanced Malware Detection – Signatures vs. Behavior Analysis
ChatGPT and Malware Analysis - ThreatMon - ThreatMon Blog

Malware detection - Use cases · Wazuh documentation
Sandbox Kaspersky

Malware Analysis: Tips, Tools, and Techniques