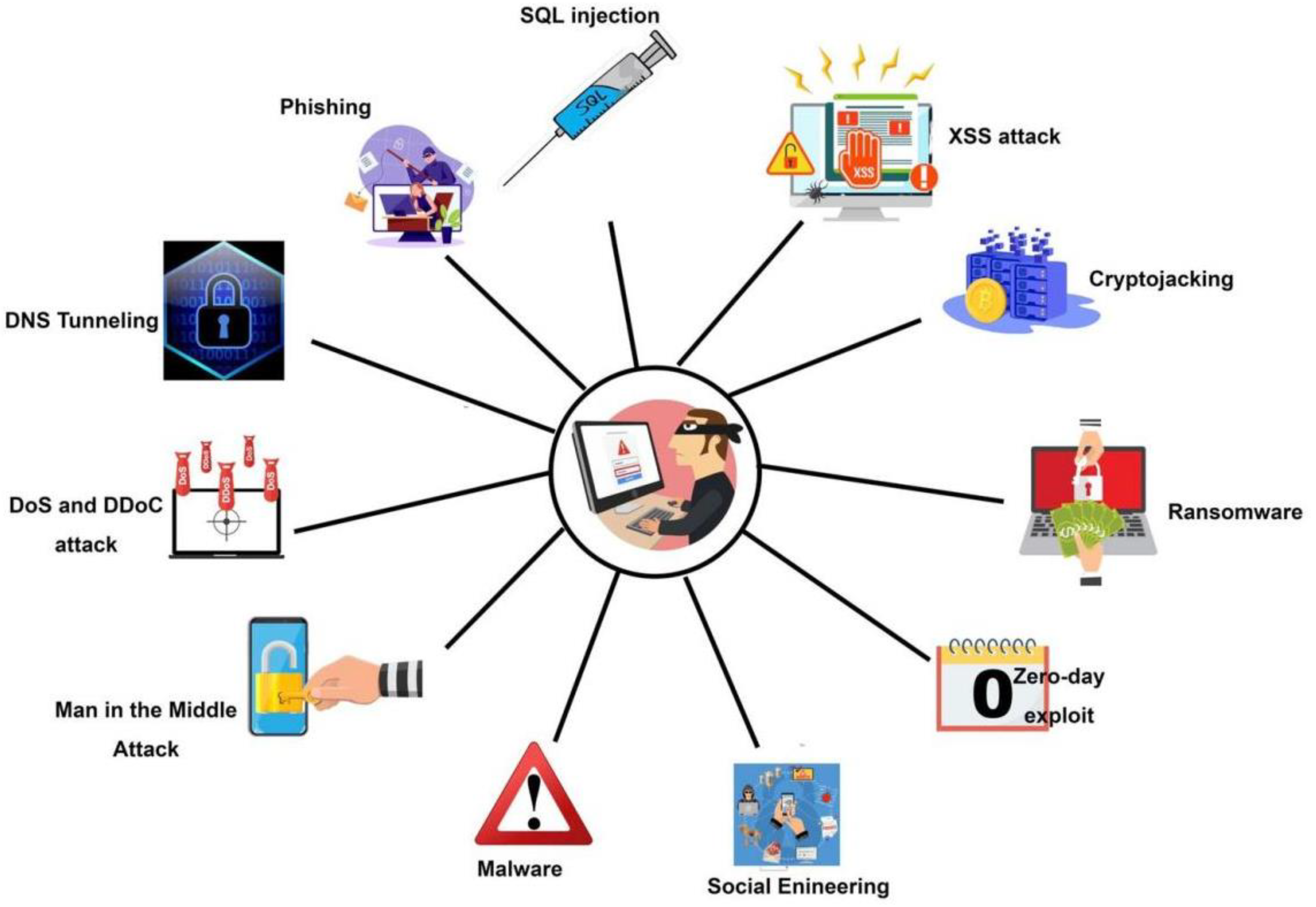
Malware analysis Malicious activity
5
$ 23.50
In stock
(670)
Product Description
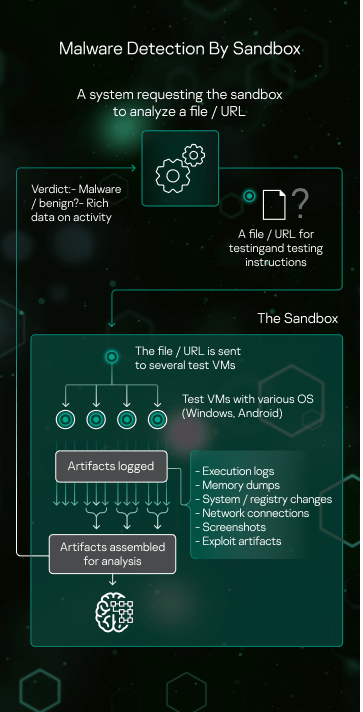
Sandbox Kaspersky
Symmetry, Free Full-Text

2: Block diagram of malware detection and classification system
Malware Detection: 7 Methods and Security Solutions that Use Them
Virtualization/Sandbox Evasion - How Attackers Avoid Malware Analysis

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights
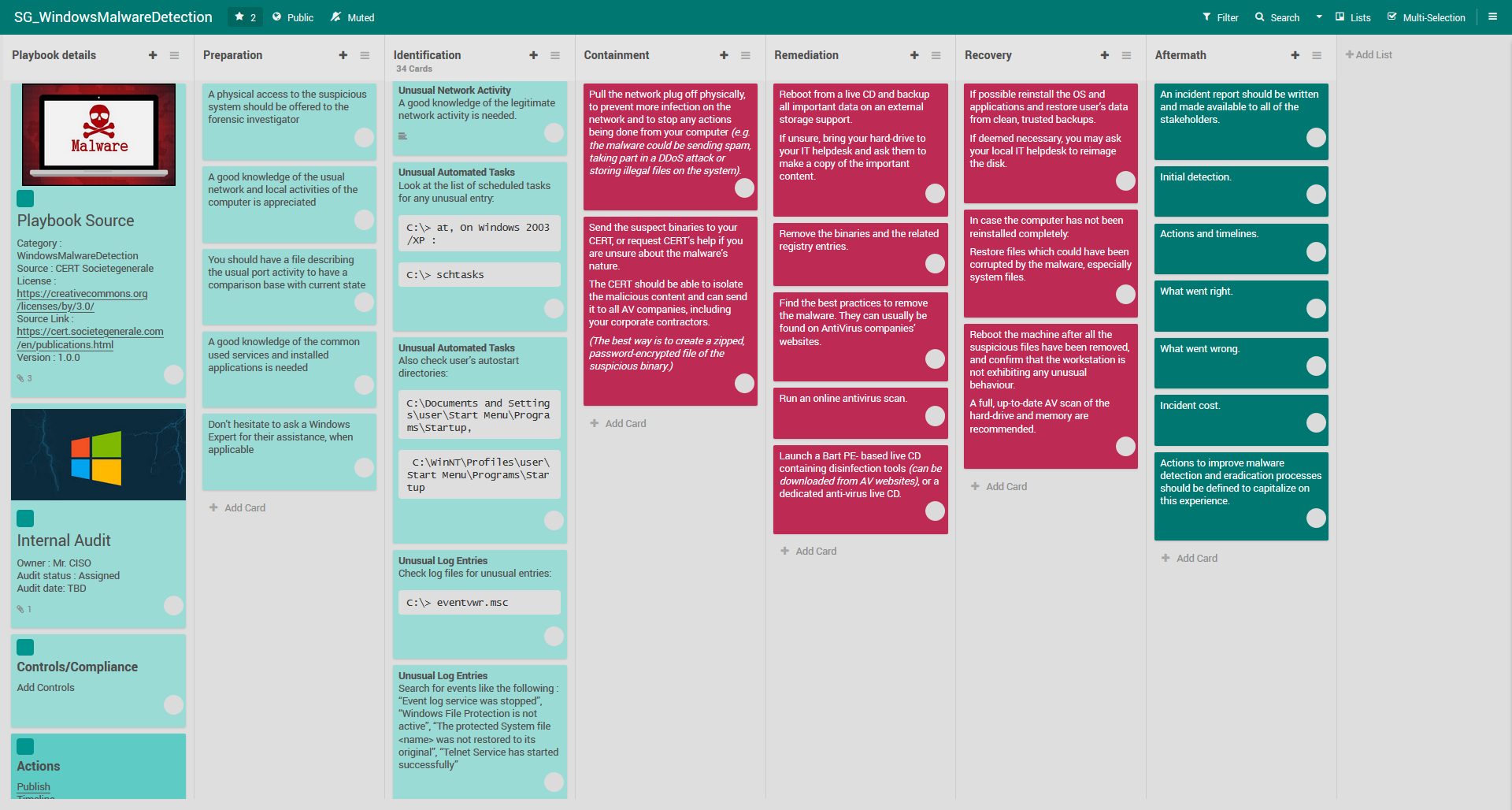
Playbook for Malware outbreak

Behavior-based malware analysis process as conducted by our
ChatGPT and Malware Analysis - ThreatMon - ThreatMon Blog

The Role of Malware Analysis in Cybersecurity
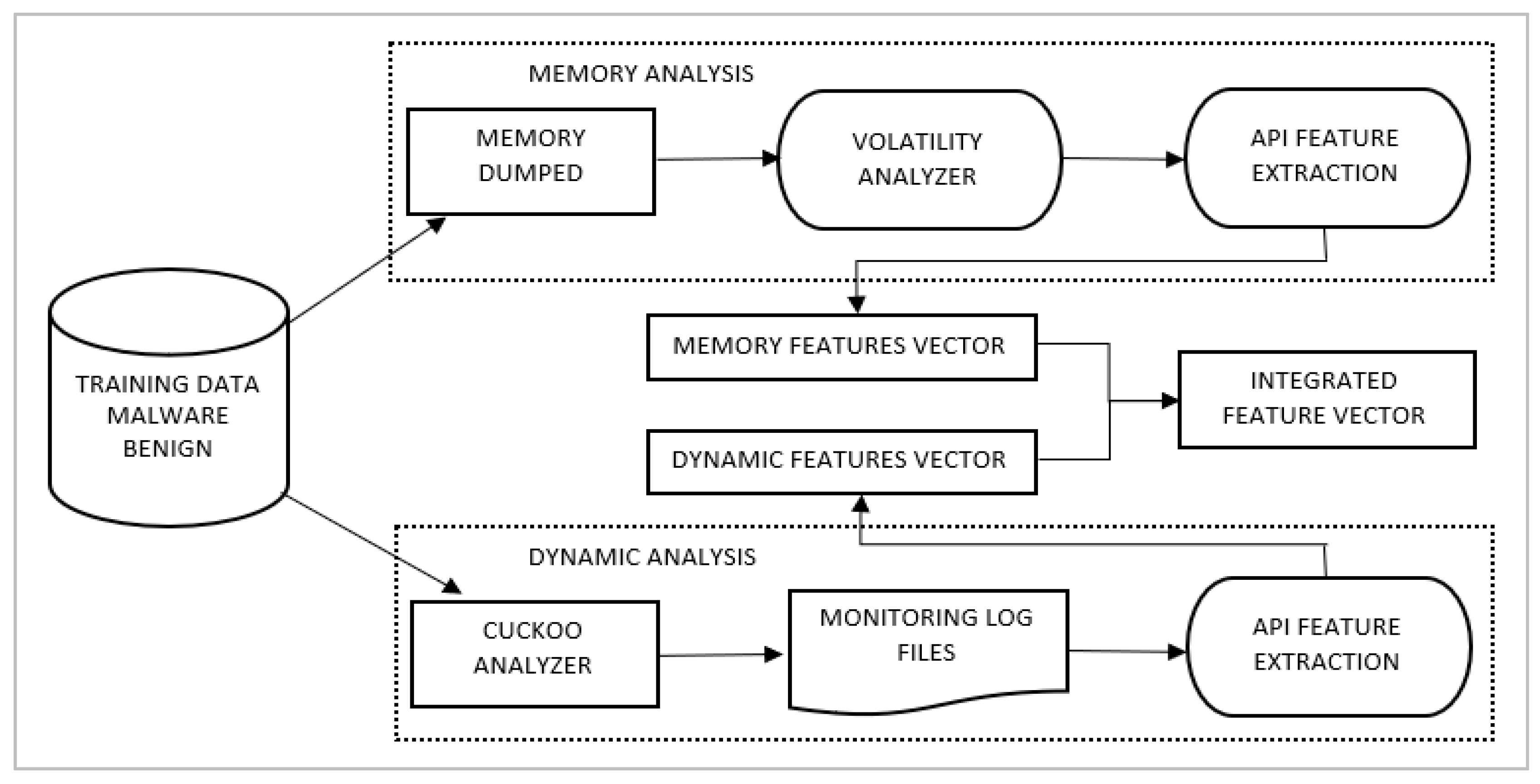
Applied Sciences, Free Full-Text
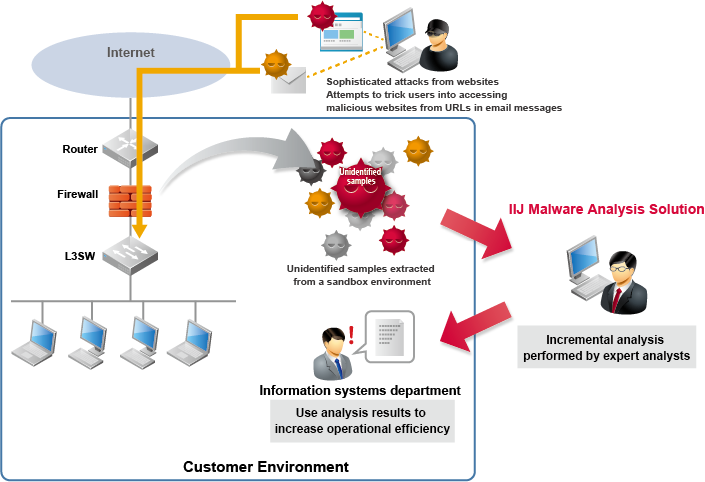
IIJ Malware Analysis Solution, Business

Malware Analysis Of Malicious Documents

Malware Analysis Solutions - Fast & Accurate Detection - OPSWAT
Process flowchart of the malware analysis process during the experiment