Malware analysis Malicious activity
4.5
$ 24.00
In stock
(150)
Product Description
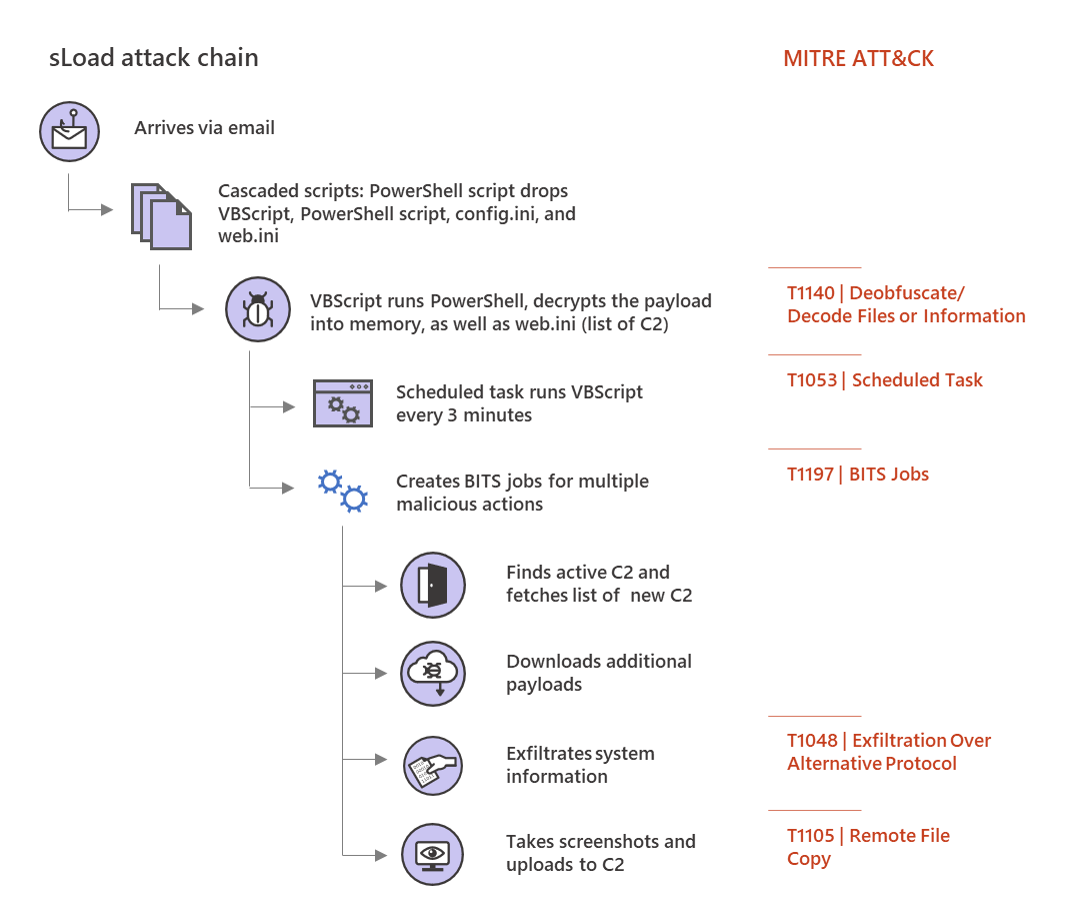
Multi-stage downloader Trojan sLoad abuses BITS almost exclusively for malicious activities
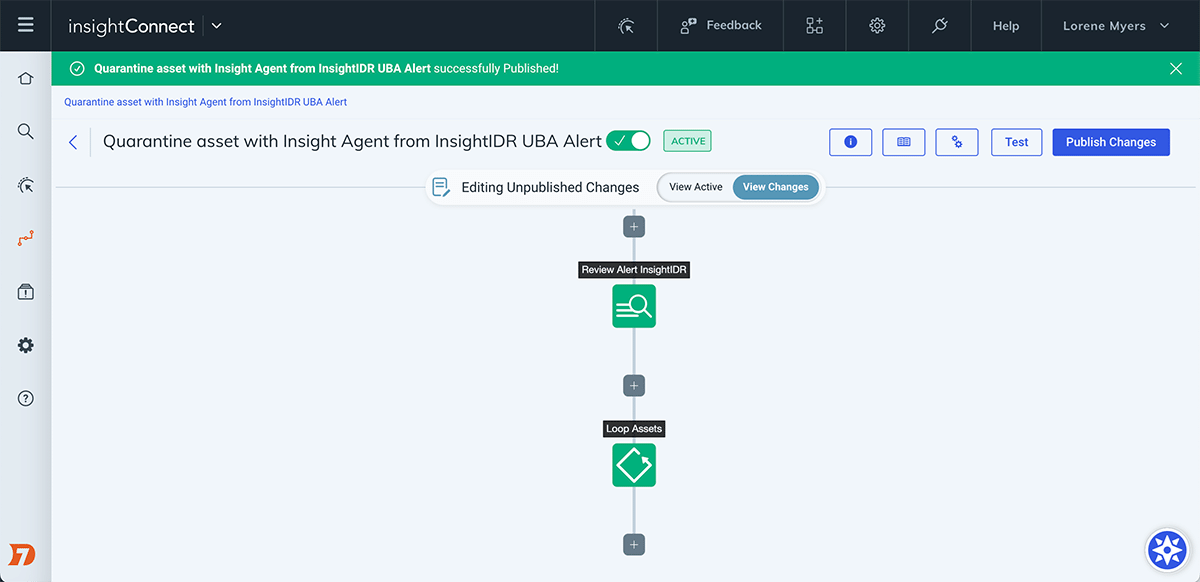
Automate the Investigation and Containment of Malware: InsightConnect
Applied Sciences, Free Full-Text
Malware Detection: 7 Methods and Security Solutions that Use Them
Symmetry, Free Full-Text
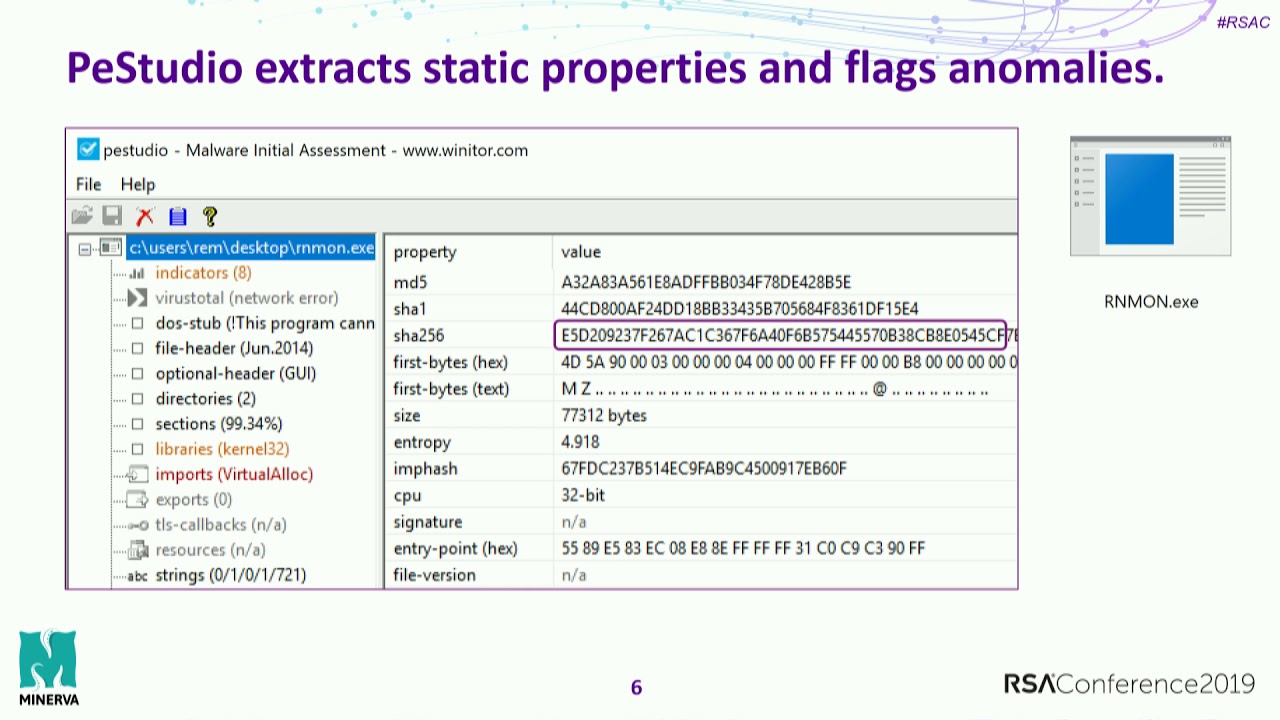
Practical Malware Analysis Essentials for Incident Responders

What to Include in a Malware Analysis Report

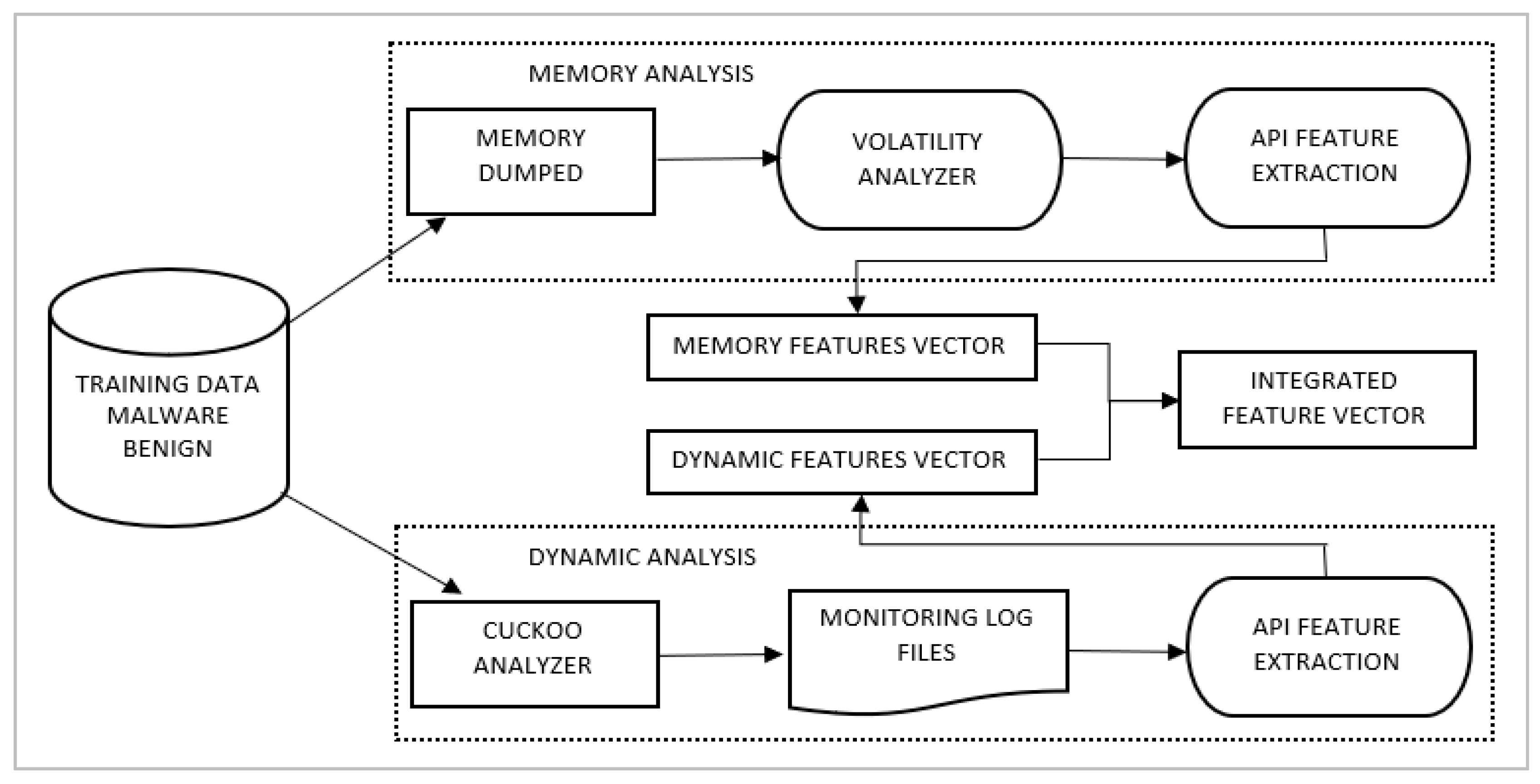
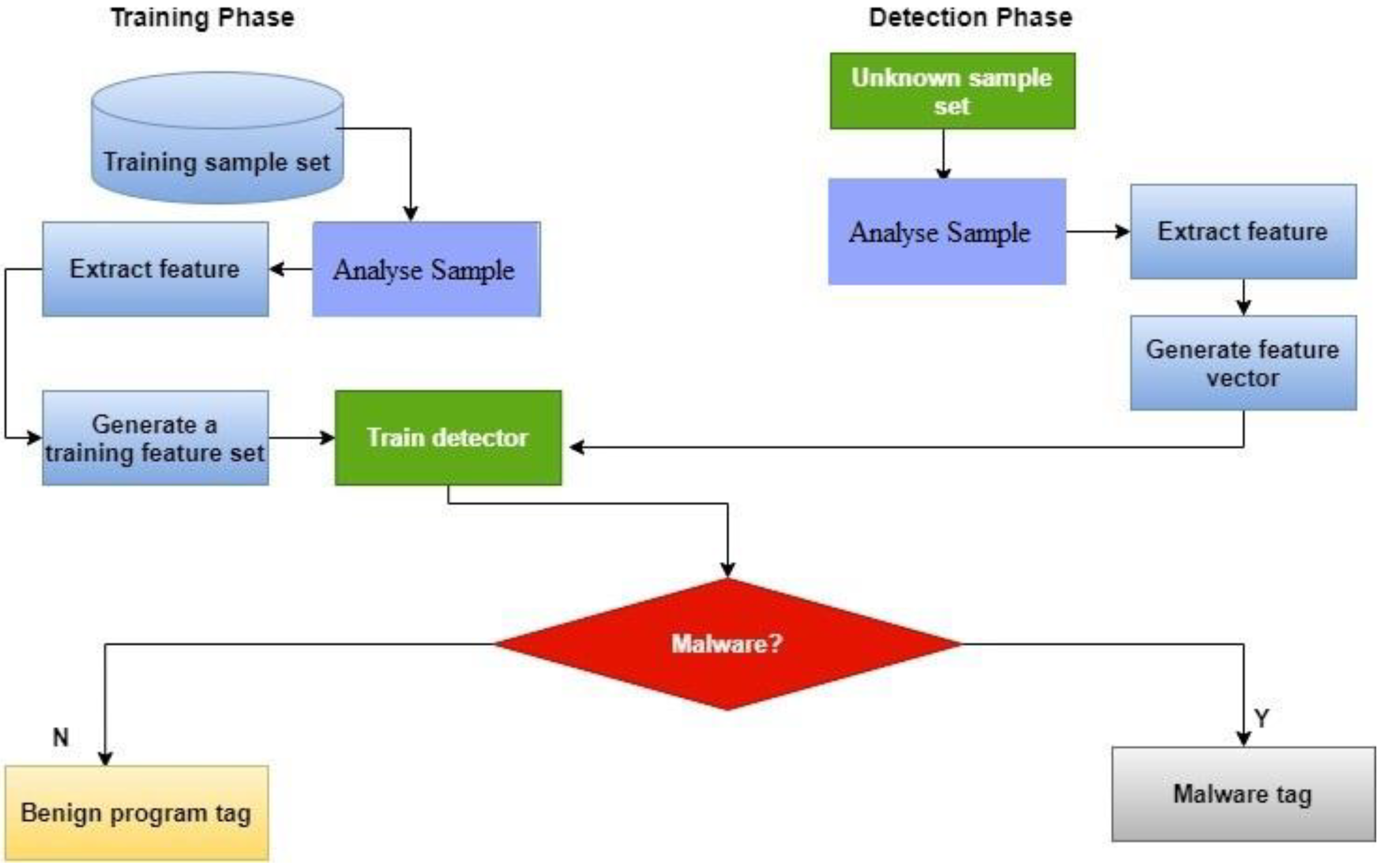
2: Block diagram of malware detection and classification system
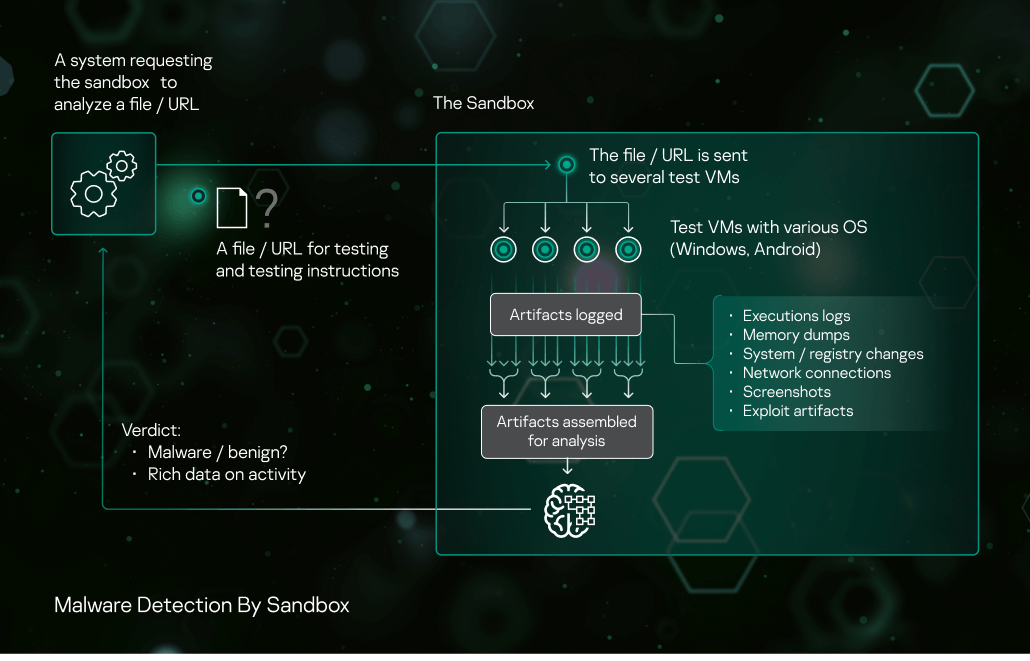
Sandbox Kaspersky

Malware Analysis Benefits Incident Response
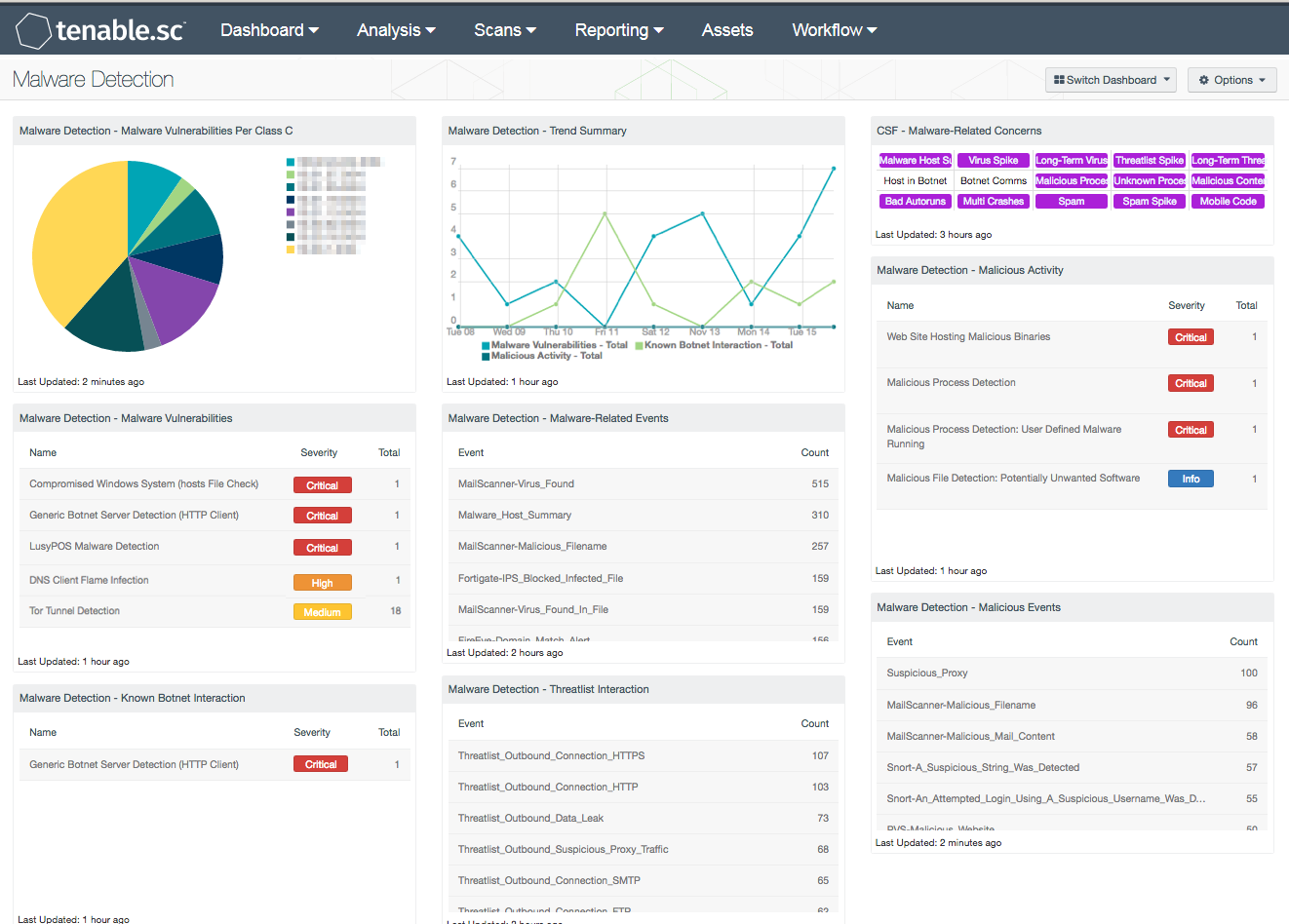
Malware Detection - SC Dashboard

The Differences Between Static and Dynamic Malware Analysis