Analysis Malicious activity
4.9
$ 26.50
In stock
(462)
Product Description
Highlight, take notes, and search in the book

Practical Memory Forensics: Jumpstart effective forensic analysis of volatile memory

PDF) Enterprise Network Infrastructure Malicious Activity Analysis

Malicious Activity Reports: Detailed Analysis of Cyber Threats

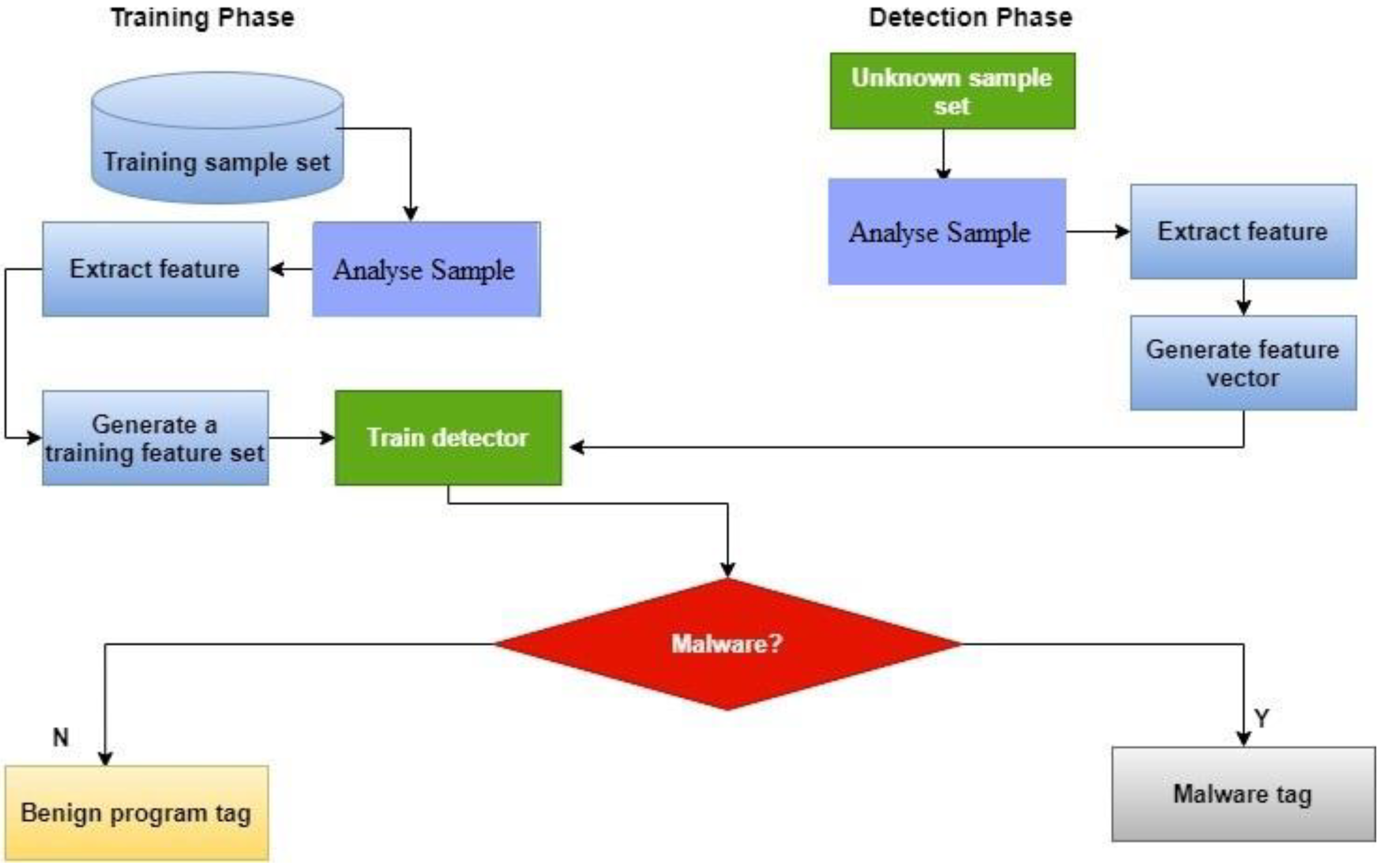
Security Orchestration Use Case: Automating Malware Analysis

PDF) Malware Automatic Analysis Cesar Andrade and Claudio de

Dynamic Malware Analysis in the Modern Era—A State of the Art
Symmetry, Free Full-Text
7 Best Malware Detection & Analysis Tools for Networks in 2023

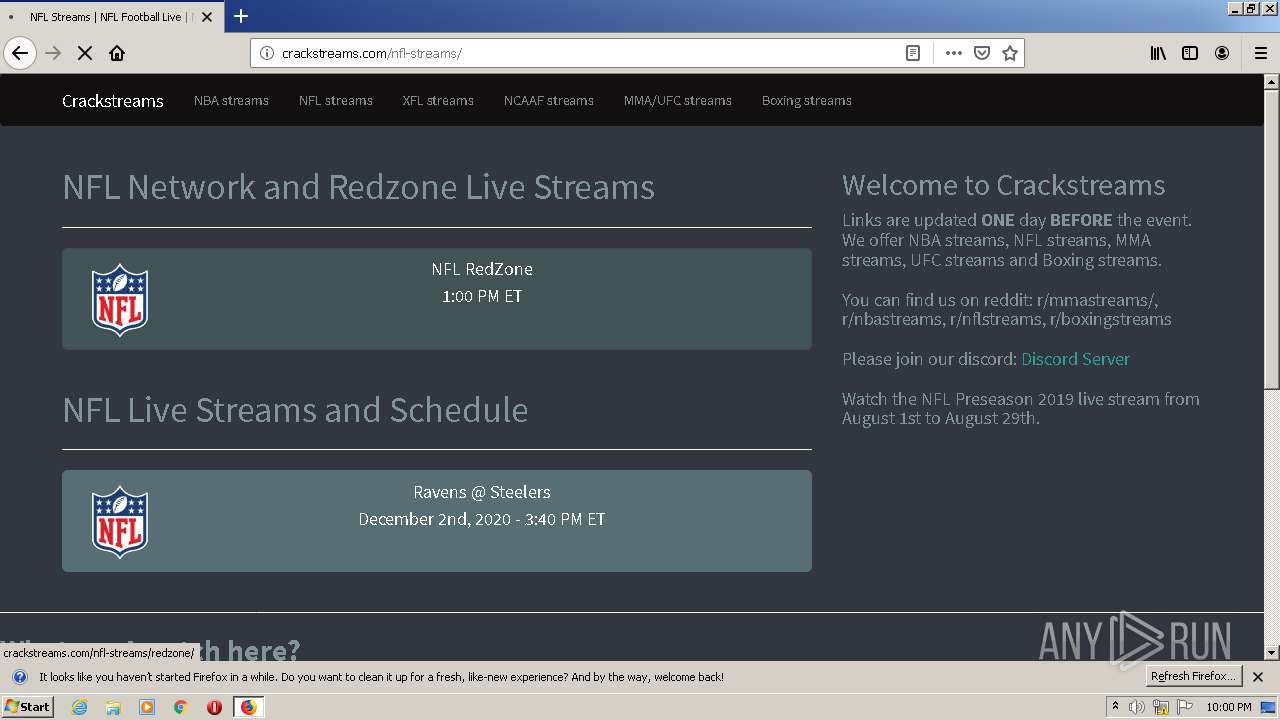
Malicious activity analysis from BYOD endpoint using SandBlast